$320M No Joke – Another Crypto Hack, Another Bitter Truth
Another theft in the cryptocurrency community – and a threat to crypto going mainstream – is a recent crypto hack. Hundreds of millions of dollars were stolen. How much money will be involved in the next heist?
Author:James PierceReviewer:Camilo WoodFeb 15, 20225.2K Shares348.2K Views

The year 2022 kicked off with a promising start for cryptocurrency when two American companies joined forces in January to make crypto become mainstream, but a crypto hack this February rekindled long-standing security concerns.
Mainstream media and various tech websites and crypto online sources reported about the stolen 120,000 wrapped Ether (WETH), with an estimated value of $320 million.
The latest victim was Wormhole and involved the Ethereum and Solana blockchains.
Wormhole is an interoperability protocol that allows users to move their digital assets (e.g., cryptocurrencies and non-fungible tokens or NFTs) from one blockchain to another. Aside from Ethereum and Solana, it also supports these other blockchains: Avalanche, Binance Smart Chain, Oasis, Polygon, and Terra.
Per Reuters, a similar case preceded this recent crypto hack, where a hacker/hackers stole coins worth approximately $600 million from Poly Network, a cryptocurrency platform, in August 2021.
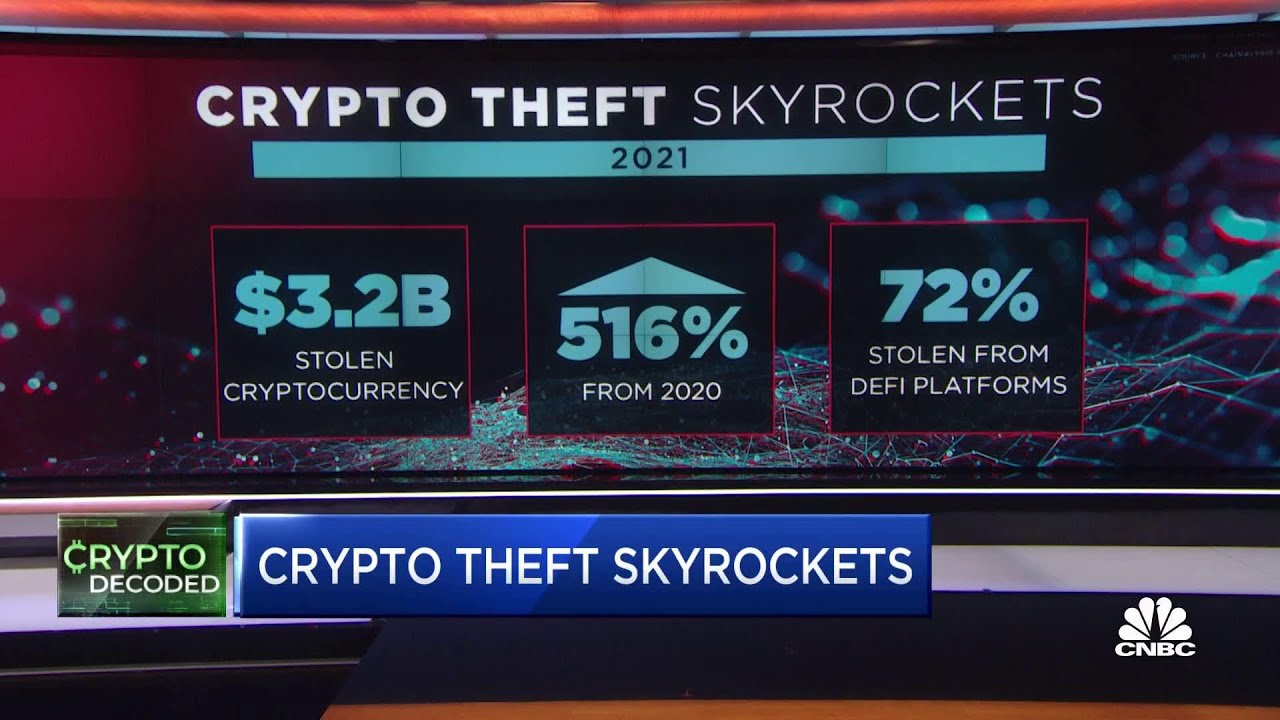
$3.2 billion in cryptocurrencies stolen during 2021
Crypto Hack
Incidents of a crypto hack never escape the radar of cryptocurrency traders and the crypto community in general.
At Hacker News, users deliberated on it. Various but correlated issues were raised, from the fundamentals of cryptocurrency to how to secure one’s coins.
One personality that even got dragged in the conversation was no less than the elusive and mysterious (or fictitious?) Satoshi Nakamoto. It appears that Bitcoin’s supposed creator will continually remain relevant.
Since the latest crypto hack involved an insane amount of money, some talked about how could the hacker(s), given that it’s stolen money, be able to literally get away with it. Like, how many briefcases will be needed to store all that money? Will they all fit in just one car?
Some users mentioned about laundering, which, for them, was the only probable way the hacker(s) could stash away some $320 million in the form of cash. Cash because as digital coins, the hacker(s) can only use them virtually to buy NFTs, as one user pointed out.
“Tainted” (stolen) coins, according to one user, could be traced and be blacklisted; therefore, it would be difficult to convert cryptocurrencies into cash. Still, one user said that it could be done through “P2P exchange” and another one mentioned “coin swap contracts.” A huge amount of money will be involved (for transaction fees/gas) to do so. But if you’re talking about $320 million, it will all be worth it, according to them.
In a separate but related Hacker News thread, several comments focused on regulations observed by financial institutions – the same regulations that blockchain distances itself from. These regulations could avert a crypto hack as well as aid victims in hunting down the perpetrators and putting them behind bars. Some argued that blockchain wants to reinvent the wheel in the first place.
One user even said that Satoshi Nakamoto might be just “a public administration professor,” who wants to make the crypto community realize why banks implement certain regulations. What else but for security purposes.
If a crypto hack happens online, is it possible to carry out a cryptocurrency heist in the physical world sans the participation of hackers?
What Is Multisig In Crypto?
Perhaps the foremost concern – or at least one of the principal concerns – raised among the Hacker News users in the aftermath of the Wormhole crypto hack was on security.
One user commented about the probability of non-hackers to resort to old fashioned physical assaults and violent threats in order to get their hands on someone else’s passwords. Based on two references provided by another user, such an incident already happened, where instead of a computer, a gun was used.
In 2018, crypto trader Danny Aston from South Oxfordshire District in England transferred Bitcoins – at gunpoint, according to CoinDesk. Newsweek reported that American millionaire tech entrepreneur Zaryn Dentzel learned it the hard way, when men entered his house in Spain in 2021. They covered Dentzel’s eyes, beat him up, and used a Taser on him – just for him to give the password to his Bitcoin account.
Moreover, if a crypto hack couldn’t be prevented, filing a police report and eventually a lawsuit are two more concerns, with both being tedious to do, as revealed by one user. Some users even wondered if law enforcement agencies, including the FBIalready handled similar cases in the past. If ever they did, what’s the outcome, anyway?
One user commented that a crypto hack could be the “perfect crime” because it seems “no one has been arrested” so far for committing it. Another user indirectly agreed by saying that the hacker(s) behind the Wormhole crypto hack can use Tornado Cash.
CoinDesk stated that through Tornado Cash, users can “obfuscate their digital trail on the Ethereum blockchain.”
Hence, believing that an ounce of prevention is worth a pound of cure, some users recommended using a multisig.
Multisignature cryptocurrency wallets (multisignature wallets or multisigs) work like a bank vault that can only be opened using multiple keys, according to CoinDesk. Apparently, the job of a multisig is to safeguard one’s coins.
Another cybersecurity measure to deter a crypto hack, as suggested by one user, is to adopt the “multi-day settlement” practiced by business communities in the real world. To this user, processing money worth millions of dollars shouldn’t be “instantaneous.”
Conclusion
Going back to the crypto hack on Wormhole, on February 5, it announced via Twitter about its $10 million reward for anyone who will return the stolen funds. It initially launched a “bug bounty” to the tune of $3.5 million.
Several news sites quoted Ronghui Gu, an assistant professor of Computer Science at Columbia University and co-founder of CertiK, a New York-based blockchain cybersecurity company, regarding his reaction to the said incident.
“This attack is sounding the alarms of growing concern around security on the blockchain,” said Gu.
If a crypto hack is inevitable and capturing the culprits is already an uphill climb, then probably high time to reassess crypto regulations and reexamine blockchain security issues.

James Pierce
Author

Camilo Wood
Reviewer
Latest Articles
Popular Articles


